Ajay Angdembe
IT built for environments that don't blink: regulated, multi-site, 24/7. Identity, cloud, network, endpoint, and perimeter owned end-to-end. Master's in IT, CompTIA Security+ certified, seven years across healthcare, higher ed, and MSP, backed by a production homelab held to the same security bar.
System Administration

Ground-up IT build for a 4-clinic healthcare org. No centralized infrastructure, no identity controls, no documentation. One hire to design, build, and run the entire stack.
From Helpdesk to Cloud
 CompTIA Security+
May 2026
NEW
CompTIA Security+
May 2026
NEW
 CCNA 200-301
in progress · Target Aug 2026
CCNA 200-301
in progress · Target Aug 2026
MSP & Multi-Tenant Operations
- Tier 1-3 remote and onsite support across 120+ SMB clients in multiple industries
- 45-minute SLA target with 99.9% client uptime, full ticket lifecycle in ConnectWise
- Networking specialist role: firewall policy, AP, VPN, licensing across multi-tenant
- Break/Fix to Tier 1-3 escalation model, quarterly ATRs and DR drills
IT Support & Endpoint Operations
- Tier 1-3 support across 300+ endpoints under strict SLA
- Autopilot, SCCM, MDT, Intune mass deployments and PXE imaging
- Trend Micro and Webroot endpoint protection, WSUS patch management
- Multi-platform fleet: Windows 10/11, Server 2012-2022, macOS, iOS, iPadOS, Android


Identity, Access & Security
- AD, Entra ID, Group Policy, and SSO across hybrid environments
- MFA, conditional access, RBAC for HIPAA-regulated staff
- Hybrid identity sync via Azure AD Connect, break-glass and trusted-location CA policies
- ZixEncrypt and Defender aligned to Zero Trust
Microsoft 365 & Cloud Infrastructure
- Full M365 tenant for 4 healthcare sites: E3/E5, Exchange Online, Teams, SharePoint Online, OneDrive
- Real-time monitoring of Defender, Entra ID sign-ins, ConnectWise
- DNS, DHCP, domain, file share ops on Windows Server

Backup, Recovery & Automation
- VMware vCenter/ESXi and Hyper-V virtualization, maintenance and recoverability
- Veeam, Acronis, Dropsuite backups with recovery testing
- DR playbooks rehearsed quarterly for realistic RPO/RTO
- PowerShell automation for provisioning and cleanup
Network & Wireless Engineering
- 6-segment VLAN architecture with 802.1Q trunking, L2/L3 switching, pfSense firewall rules
- SonicWall firewall management, Aruba and Cisco AP deployments, Avaya VoIP across 3 sites
- ISP failover coordination, site-to-site WireGuard tunnels, Suricata IDS for perimeter visibility

My Projects
Builds, writing, and videos. The work behind the resume.
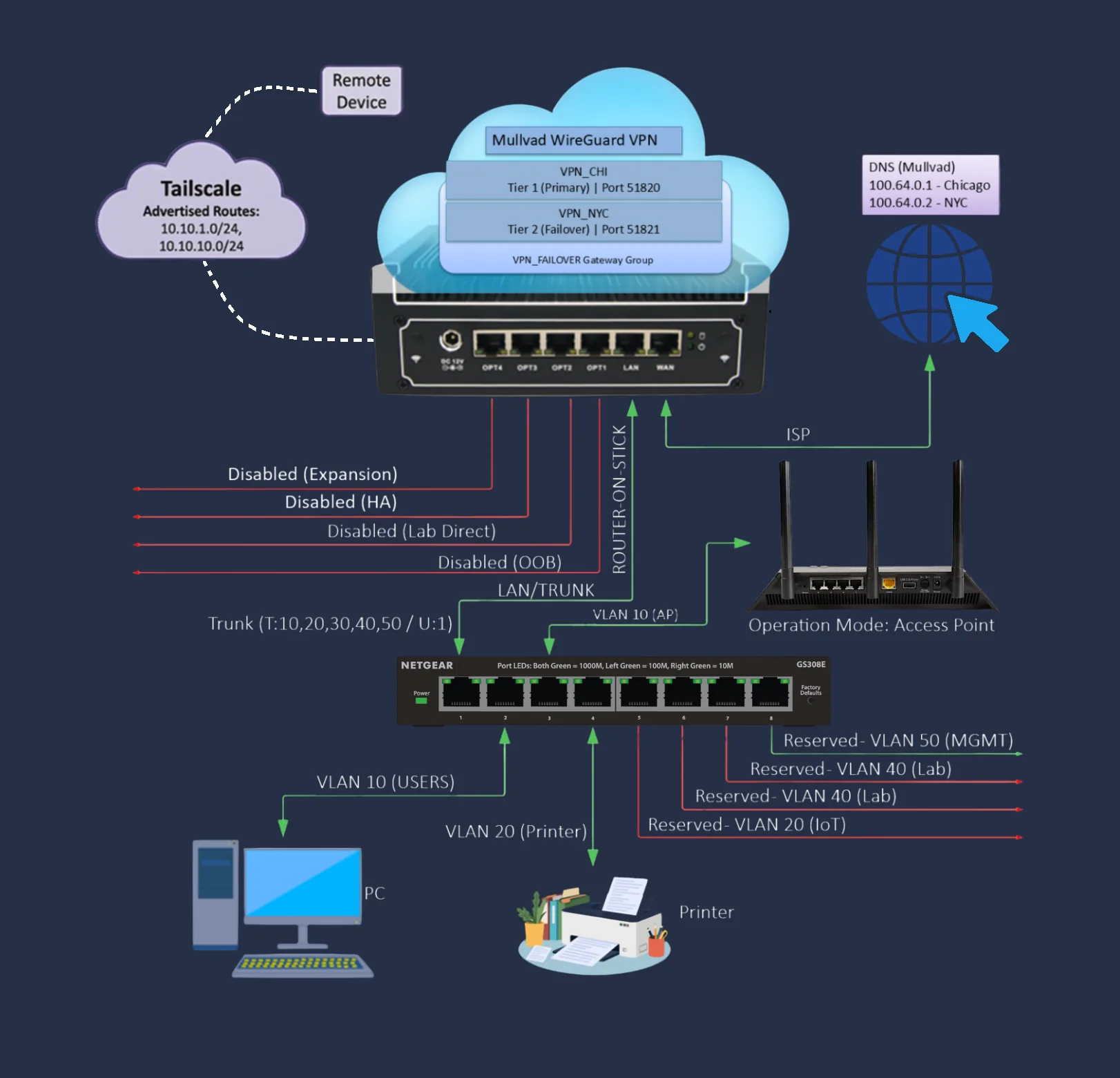
Router-on-a-Stick Homelab
A 2024+ weekend build that mirrors enterprise patterns at home. Multi-VLAN segmentation, intrusion detection, VPN failover, and a documented kill-switch policy. Full architecture, switch and firewall manuals, and rack walkthrough live on the inner page.
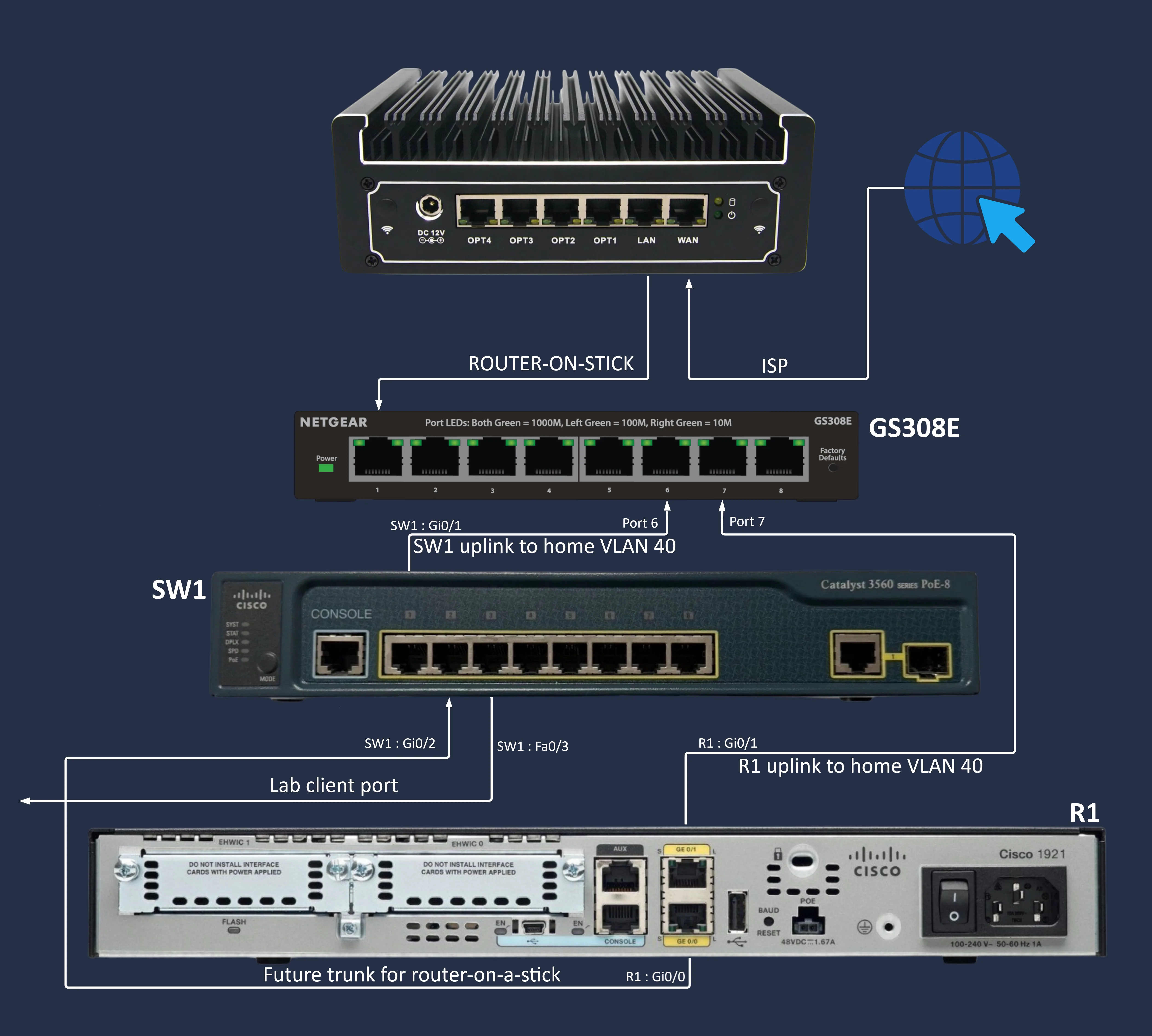
CCNA Lab
Hands-on Cisco IOS labs preparing for the Aug 2026 CCNA exam. VLAN configuration, trunk ports, inter-VLAN routing, and ACL exercises on Catalyst 3560 PoE 8 and Cisco 1900 series router.
Research Articles
Original writing on networking, security, and the work behind the resume. First paper live: Privacy is a Property, Not a Feature: a privacy-first homelab on pfSense with dual-VPN failover, six VLANs, IDS, and a verified kill switch. More papers in the roadmap.
Read research →Find Jobs
Most H1B job seekers are applying blind. This changes that. A verified database of 65,000 employers, 3.7M+ approvals, 50 states + DC, built from 15 years of official USCIS data (2009 to 2023), organized by state and industry, cap-exempt orgs flagged. Paired with a complete search strategy and workflow.
Open the H1B Database →Personal Vlog
Tinkering with networks and electronics at the bench, books on the nightstand, food on the stove. Slow walks through the work and life behind it.
In productionLet's Work Together
Looking for a System Administrator or Network Engineer who builds systems that last.
Based in Minnesota. Open to local, remote, and hybrid roles. Available for immediate conversation.
Visa sponsorship required; targeting H1B cap exempt employers. Healthcare systems, university research, and nonprofit research preferred.
Email is the fastest way to reach me. Replies within 1-2 business days.
Best for scoping a role, talking through what end-to-end IT ownership looks like in your environment, or sanity-checking a security baseline.
CompTIA Security+ certified (May 2026). Cisco lab work since 2017; pfSense build since 2024.


